Identity assurance, procurement 2

...within this value. More information including background to the programme can be found on our blog. Details on the standards and technical requirements can be found in our good practice...

...within this value. More information including background to the programme can be found on our blog. Details on the standards and technical requirements can be found in our good practice...
...and gender (if you chose to provide it). See Adam's post about how the technical architecture protects people's privacy for more information about how that works. Where to find more...

...but, for now, it remains one to watch and experiment with, rather than one to implement wholesale. Adam Cooper is GOV.UK Verify’s Technical Architect. You can follow him on Twitter....
When we designed the identity assurance architecture we wanted to protect users from identity theft and fraud, to secure their data as it is used online, and to reduce the...
...of anonymity, data minimisation and user control are baked into the underlying technical and commercial models. There will always be areas where we are obliged to retain or share data...
...to bring documents and information with them guidance on what technical user support is available from identity providers for all users It’s important that each service is aware of the...
This post is an introduction to the document checking service, part of GOV.UK Verify's technical architecture. If you're interested in the different documents and methods certified companies can use to...
...use identity assurance service’s technical requirements and operational standards information about how the document checking service works information about how procurement 2 tenders will be evaluated Please use this dedicated...
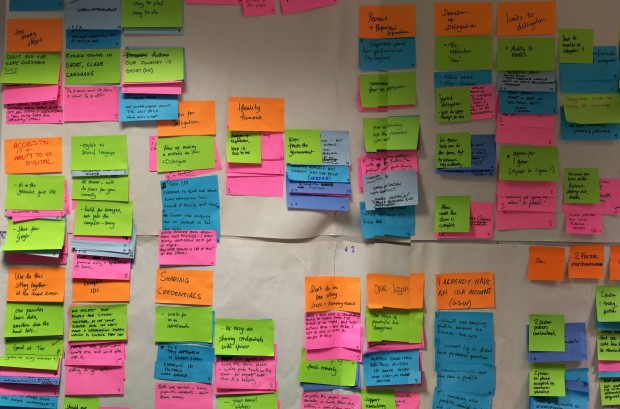
...alpha projects. The team We set up a discovery team that included technical architecture, business analysis and user research. We also included representatives from HMRC and DWP - two of...

This post provides an update on the work that local authorities and GDS have done together through the Open Identity Exchange (OIX) on citizen identity needs for local authority services....