Search results for VIPREG betwinner promo code no deposit El Salvador
...shared library of code used for our SAML (Security Assertion Markup Language) messages. This removes dependencies between our microservices and will allow us to make changes to our code faster....
...transfer skills throughout the team. It also produces high quality, maintainable code. In situations where it doesn't make sense to pair, we ensure peer review as a minimum to see...
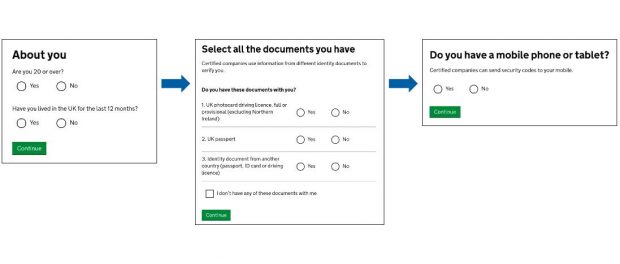
...second step can be a code sent to a mobile phone (one of the more commonly used methods), or it can be another method such as a code communicated to...
...and keyboard while the rest of the mob act as ‘navigators’ by suggesting what source code needs to be produced. Not everybody will be part of the mob at all...
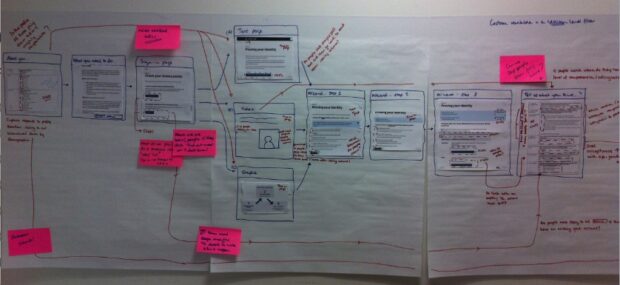
...pages (e.g. clicks made on links) and extra tagging code called custom variables which enabled us to segment the data. We also added an extra step into the process: when...
...Commissioner’s Code of Practice for Privacy Impact Assessments provides an excellent proposed methodology for a PIA, which was used as a starting point for the review of GOV.UK Verify. Conducting...
...skipping through sections that the screen reading software identifies using the header tags in the code. However, we realised that some of the pages in GOV.UK Verify don’t use headers...
...we knew our time in the room with the assessors would be limited; blogging helped us clarify our own thoughts, and gave the panel access to a lot of information...
...code we used simplify the technical onboarding of new services by centralising the location of certain assets maintain and improve the service continue recruiting new members for the technical delivery...
...phone or a landline are now able to complete verification - for example, by downloading a code to their computer. This means that everyone can now progress past the second...